ClawNex
ClawNex
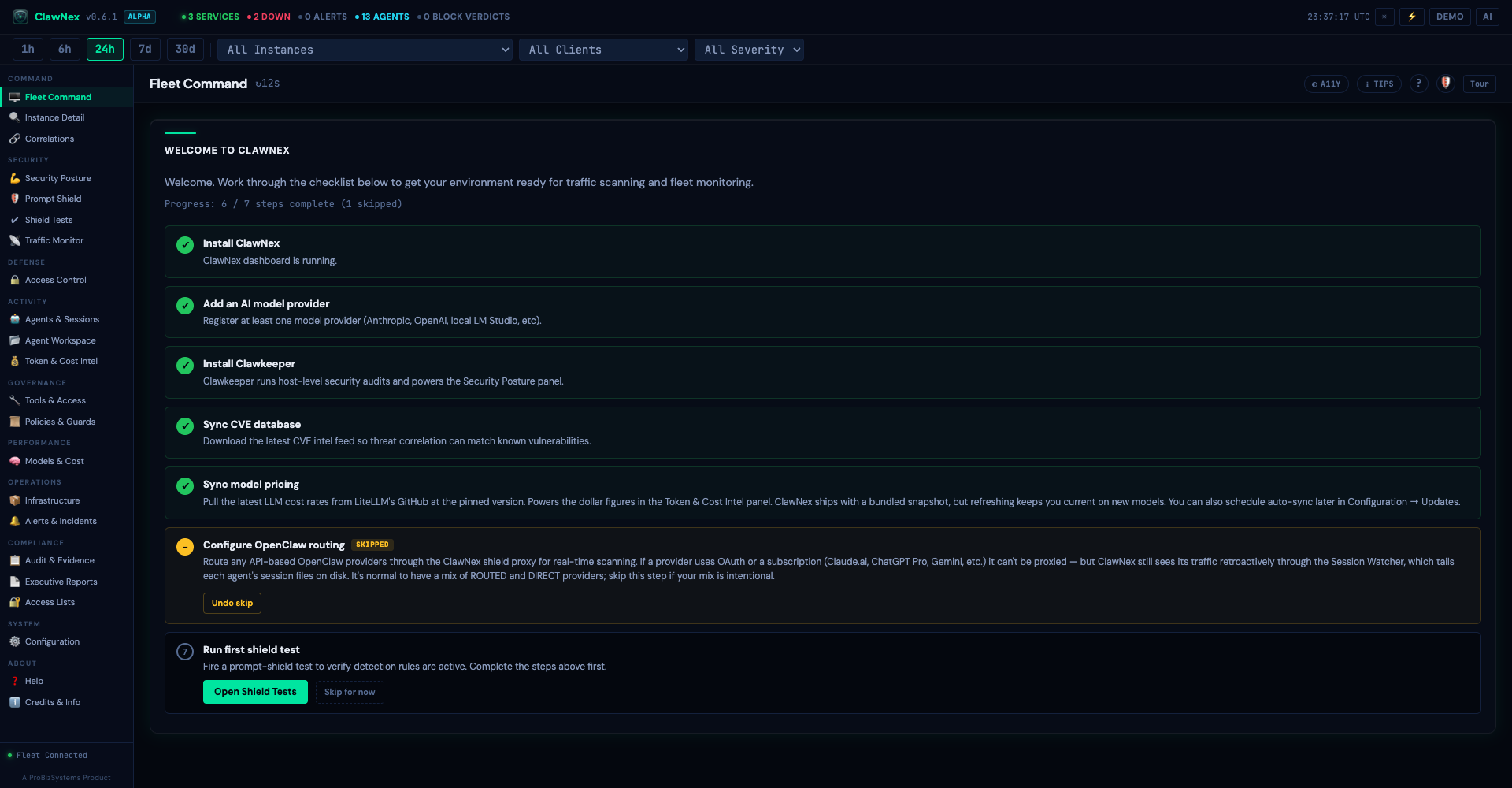
Runtime security for AI agent fleets.
See, scan, and control every conversation your AI agents have with language models. Know who can reach what, what they can do, and where blast radius starts.
AI agents don't just answer anymore — they act. ClawNex gives security teams visibility and control before that becomes a liability.